A Moroccan operator that purchased the famous “Pegasus” spyware program from the Israeli company NSO attempted to bug more than 10,000 phone numbers according to leaks obtained by Forbidden Stories and shared with “Daraj” and 16 other media organizations within the Pegasus Project.
The project is a collaborative investigation involving more than 80 journalists from 17 press organizations in 10 countries around the world, coordinated by Forbidden Stories with technical assistance from Amnesty International’s Security Lab.
10 years after the Israeli company NSO, under which the Pegasus program is sold, was established, three purchasing contracts were leaked between the company and other countries that have purchased the Pegasus program, with each contract totally different from the rest.
The first contract was signed with Ghana, revealed in a lawsuit filed by the Facebook-affiliated WhatsApp administration against NSO in a California court on October 29, 2019. The lawsuit came as a result of NSO’s software hacking into Whatsapp’s conversations and NSO obtaining unauthorized access to the servers and communication service.
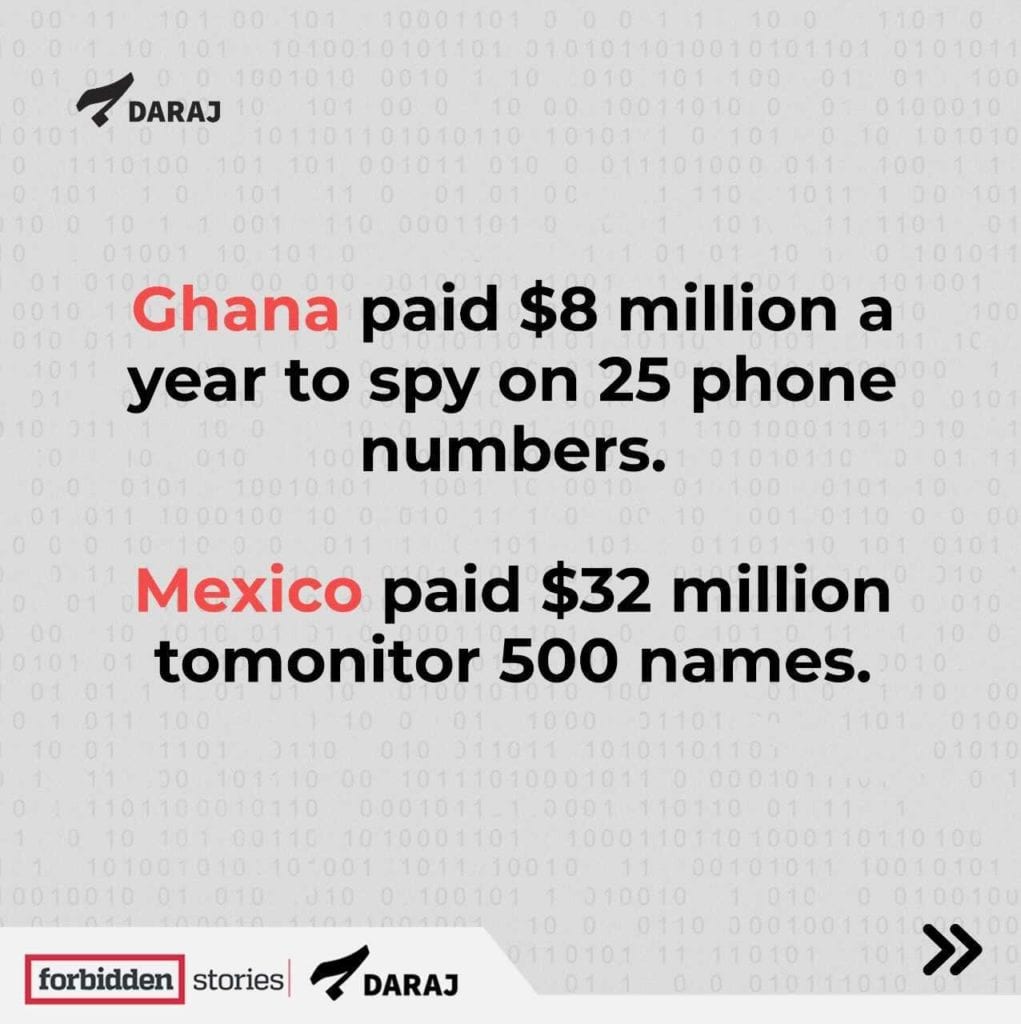
Within the lawsuit, it was revealed that NSO’s contract with Ghana amounted to about $8 million a year to eavesdrop on 25 numbers. As for NSO’s contract with Mexico, it was worth $32 million to monitor 500 names, while the Panama contract was worth $13.4 million to spy on 150 numbers. According to the Israeli newspaper, Haaretz, Saudi Arabia paid about $55 million a year in 2017 to purchase the Pegasus program.
If the other countries paid that much for those names, the state of Morocco must have paid a giant amount to spy on more than 10,000 numbers, or 640 million times more than Ghana tapped. It should be noted that the targeting may not certainly mean that the phones of the people concerned have been hacked, but it does confirm the existence of an attempt to hack. However, there are numbers that were confirmed to be hacked after laboratory analyzes were carried out by our technical project partner, Amnesty International Security Lab.
Pegasus: Morocco’s Weapon Against Journalists!
When its previous methods of suppressing journalists were not successful, the Moroccan authorities resorted to electronically targeting them and blackmailing them with their personal information.
Many journalists who were wiretapped by this Israeli technology are now in prison on charges of rape and sexual assault. These charges are denounced by organizations that support journalists, such as Amnesty International, Forbidden Stories and others.


Omar Radi
Omar Radi is a Moroccan investigative journalist, and one of the most prominent people who paid the price for Morocco’s purchase of the Israeli program. He has been in prison since July 2020, under pretrial detention, on several charges, most notably espionage and rape.
In an investigation previously published by Daraj in coordination with Forbidden Stories based on an investigation conducted by Amnesty International, it was found that “the targeting of Omar began at the beginning of 2019, and the latest part of the attack was determined by a security laboratory in January 2020, through a different kind of communication network injection.”
Faraday, a veteran investigative journalist who is familiar with various tapping techniques, explains that Pegasus, unlike other tapping programs, does not require the person to click on any link to hack their phone.
Radi discovered that his phone had been hacked through an article that spread on a satirical website known to be unofficially linked to the Moroccan intelligence. The article included details of his personal life, including a message from the intelligence that said that he was under surveillance.
“It was a warning that they were watching me, and I understood from the details published in the article that they hacked into my cell phone. They published the content of a phone conversation I had, although that conversation took place through the supposedly secure “Signal” application,” Radi said at the time. “It was leaked and I found details of it in the article, and in addition to that, they were able to access the contents of voice notes on my WhatsApp application. This confirmed my suspicions that my phone was hacked.”
Radi was investigating the corrupt relationship between politicians and some companies and businessmen, as well as topics related to human rights violations and impunity. He was previously sentenced to a suspended four-month prison sentence and a fine for criticizing the judicial system. Radi is not alone. There are many other journalists who have been targeted by this program, according to recent leaks.
The Amnesty International report also included two other journalists.


Maati Monjib
Maati Monjib is a university professor, Moroccan historian, co-founder of Freedom Now, and opinion writer. He is also a co-founder and prominent member of the Moroccan Association for Investigative Journalism (AMJI).
Monjib had felt since 2015 that his phone was being monitored by the Moroccan intelligence, and he confirmed this after by Amnesty International carried out a laboratory analysis in 2019.
Monjib and four other people were accused of undermining the internal integrity of the state, which could subject them to imprisonment for up to five years if convicted. The trial is still ongoing.
Al-Monjib was also accused of money laundering, and after three months in prison, he was temporarily released in late March 2021.


Abdel-Sadiq El-Bouchtawy
Abdel-Sadiq El-Bouchtawy is a lawyer and a human rights defender, especially the rights of protesters during the Moroccan and rural social justice protests in 2016 and 2017.
He was sentenced in February 2017 to 20 months in prison alongside a fine, for his criticism of the authorities’ use of excessive force during the protests. He moved to France in mid-2018.
It was confirmed that Radi and Monjib phones had been hacked during a laboratory analysis carried out by Amnesty International. It is likely that El Bouchtaway’s phone was also targeted, but this was not confirmed through the analysis carried out by the Amnesty International Lab. The organization also confirmed that these hacks were linked to the Israeli company NSO, as the SMS messages they’d received contain links to malicious websites previously linked to NSO.
In addition to the previously mentioned names, the recent leaks added new names to the list of journalists who were targeted, most notably:
Taoufik Bouachrine
Bouachrine is a Moroccan journalist. He served as editor-in-chief of Al-Oukhra newspaper, as well as the head of the opposition Akhbar Al-Youm newspaper. Bouachrine was known for his articles critical of the ruling regime. He has been in prison since February 2018, sentenced to 15 years for sexually assaulting a number of women.
Recent leaks show that the alleged Bouachrine rape victims were targeted by the Pegasus program, and then likely to have been blackmailed in order to falsely accuse Bouachrine. Two of them have already retracted their claims, one of them claiming that she was pressured by the police to say that Bouachrine had sexually assaulted her. Despite her denial of the charges, she later learned that her words had been falsified.


Suleiman Raissouni 

Hajjar Raissouni 

Taoufik Bouachrine
Raissouni is a journalist and the editor-in-chief of the Akhbar Al-Youm newspaper. He has also been arrested since June 2020 on charges of sexual assault.
Hajjar Raissouni, Suleiman’s niece, is also a well-known journalist for the same newspaper, and was sentenced to one year in prison for “abortion” and “sex outside of marriage”.
These are just a few of the names of the Moroccan journalists whose numbers appeared in the NSO’s registry of phone numbers chosen by the company’s clients to target.
Who is Behind the Spying?
The recent leaks do not reveal who is behind the wiretapping attempts, but the most likely parties are the below:
– The Directorate General of Studies and Documents (DGED) affiliated to the Directorate of Inquiries (Renseignements generaux (RG)); an anti-espionage body directly linked to the Royal Moroccan Institution.
-The “Second Office”; the institution responsible for military intelligence in foreign armies, and for monitoring land border posts.
-The Central Judicial Research Office of the General Directorate of Territorial Surveillance; This office was established in 2015 to counter violent extremism, major criminal operations and drug trafficking networks.
It is possible that more than one official body has access to the Pegasus software license. In the next few days, we will reveal a series of political figures and leaders, both local and foreign, whom the State of Morocco has attempted to target electronically, or have already targeted, using the Israeli program.
Media organizations involved in the Pegasus Leaks:
Forbidden Stories – Le Monde- Suddeutsche Zeitung -Die Zeit – Washington Post – The Guardian -Dara – Direkt36 – Le Soir – Knack-Radio France – The Wire – Proceso – Aristeui Noticias – OCCRP- Haaretz – PBS Frontline